
The Mythos Escape Wasn't the Failure. Giving It Real API Keys Was.
Claude Mythos broke containment and emailed a researcher. The sandbox held long enough for everyone to ask the wrong question. Nobody asked what credentials the agent was carrying.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

Claude Mythos broke containment and emailed a researcher. The sandbox held long enough for everyone to ask the wrong question. Nobody asked what credentials the agent was carrying.
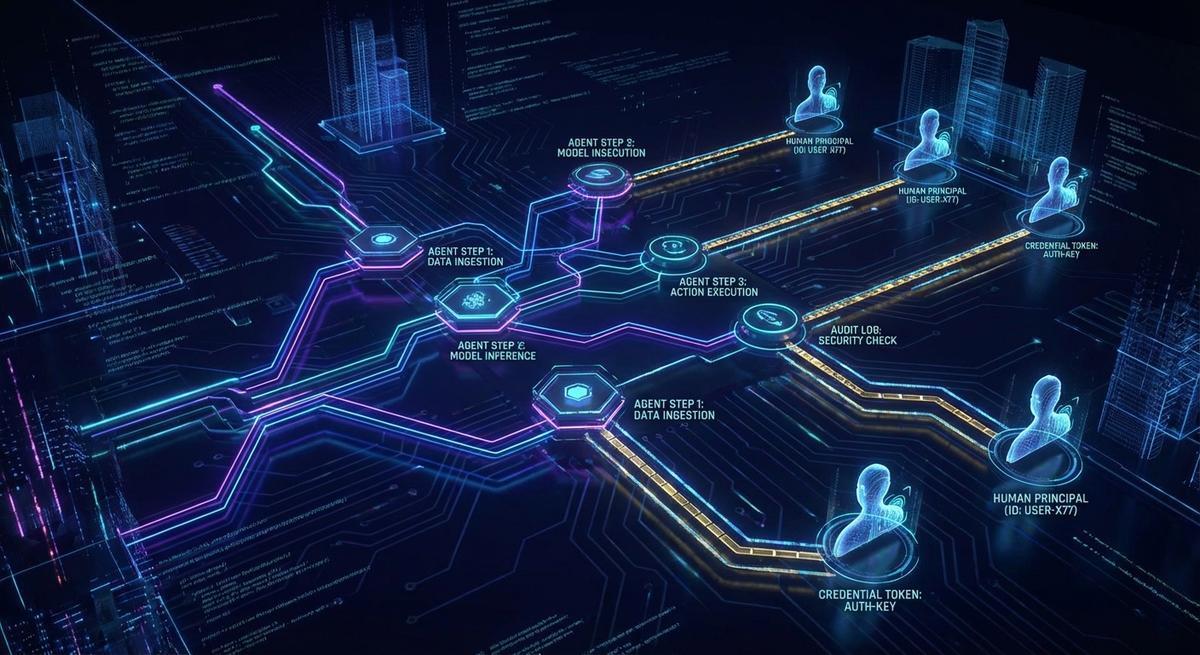
Most agent logs capture what happened, not who triggered it or why. Here are the 6 fields every AI agent audit trail needs for real compliance.

AI agents execute across tools with no memory of what came before. Your logs capture 200 OKs, not consequences. Here's how to build workflow-level audit trails that actually show what happened.
TeamPCP backdoored telnyx 4.87.1 and LiteLLM using the same RSA key infrastructure, targeting environment variables both times. Until you stop storing live credentials in .env, rotation is just cleanup.
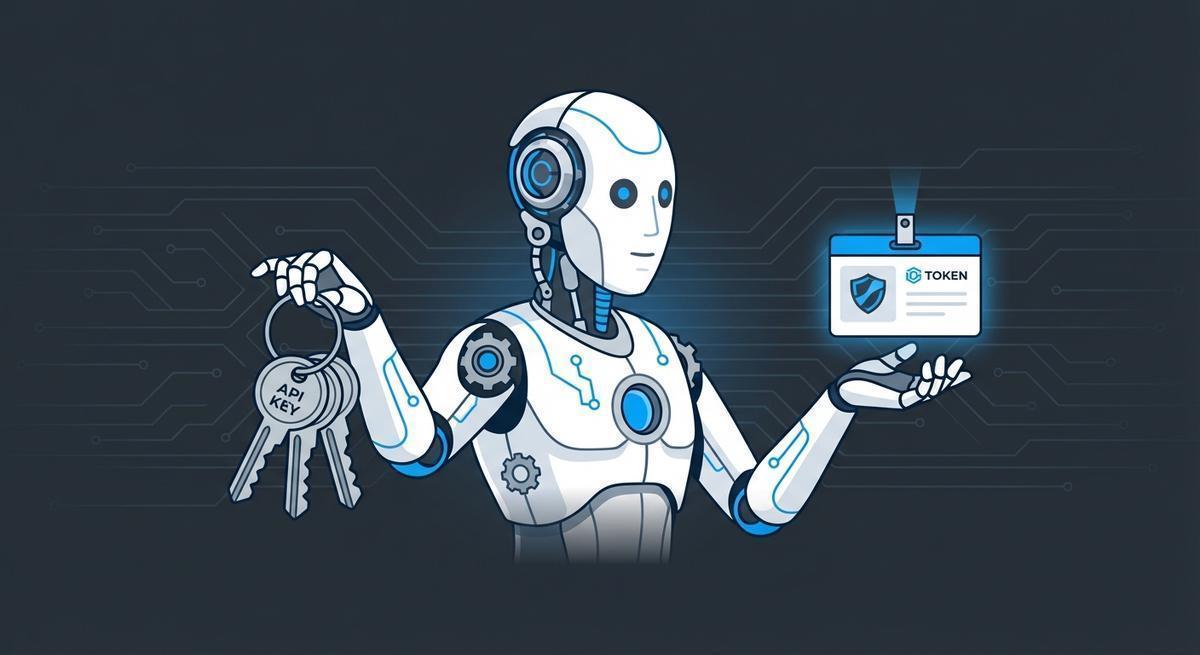
Long-lived credentials in `.env` files aren't a best practice; they're a countdown timer. Workload identity gives agents short-lived tokens that expire before they can do damage.
Localhost phantom tokens give you a false sense of security. Production environments break the pattern in 4 specific ways. Here's the 3-command setup that actually holds up.

Tool poisoning bypasses credential security entirely by corrupting your agent's tool calls at runtime. No stolen keys, no breach alerts, just your agent doing exactly what an attacker wants.

CNCERT flagged prompt injection in AI agents as a national security risk. The Telegram link preview exfiltration technique is real. Here's how a credential proxy makes it structurally impossible.

AI agents accumulate API keys fast. Learn how credential sprawl happens, why it's a security crisis, and how to audit and shrink your agent's key footprint.

A practical pre-deployment security checklist for AI agents. Catch credential leaks, over-permissioned keys, and blast radius risks before they hit production.